If you’ve ever wondered why some companies seem unshakeable when a data breach makes headlines — while others crumble — the answer often comes down to whether they have a systematic approach to information security. ISO 27001 is one of the most respected frameworks for building exactly that. But for many people, the name alone sounds intimidating.
This article breaks it down in plain language: what ISO 27001 actually is, why it was created, what it requires, and whether your organization should care about it.
Table of Contents
What Is ISO 27001?
ISO 27001 is an international standard for managing information security. Its full official name is ISO/IEC 27001:2022 — Information Security, Cybersecurity and Privacy Protection — Information Security Management Systems. It was developed jointly by two global bodies: the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC), representing over 160 countries.
At its core, ISO 27001 provides organizations with a blueprint for building and maintaining an Information Security Management System (ISMS) — a structured combination of people, processes, and technology designed to protect sensitive information from threats.
Think of it less like a software tool and more like a management philosophy. The standard tells you how to think about and organize your security efforts, not just which firewall to install.
Why Was ISO 27001 Created?
The challenge that ISO 27001 was designed to solve is a real one: different industries, countries, and sectors all have their own security regulations. Healthcare has HIPAA. The U.S. federal government uses NIST 800. Payment processors follow PCI-DSS. Financial firms deal with Sarbanes-Oxley. And nations increasingly have their own data protection laws.
For a company operating across borders — say, with offices in the U.S., Canada, and Germany — navigating this patchwork of regulations is enormously complex. ISO 27001 provides a single, internationally recognized standard that maps across these environments, giving global organizations a common language and framework for security.
Beyond compliance, the need is real. Studies have found that over 80% of U.S. companies reported their systems had been successfully hacked to steal, change, or expose sensitive data. Security cannot be an afterthought; it needs to be woven into how an organization operates. ISO 27001 exists to help organizations do exactly that.
The Three Pillars: Confidentiality, Integrity, and Availability
Everything in ISO 27001 is built around protecting three core properties of information, often called the CIA Triad:
Confidentiality means ensuring that sensitive information is only accessible to those authorized to see it. Inadequate access controls, poor encryption, and lack of employee awareness are among the most common failure points here.
Integrity refers to keeping information accurate and trustworthy. If an attacker can alter your website, modify records, or change internal data without detection, the integrity of your systems is compromised — and so is your reputation.
Availability means that information and systems are accessible when people need them. Redundant infrastructure, disaster recovery plans, and proactive software updates all contribute to maintaining availability during disruptions.
The ISMS: More Than a Stack of Documents
A common misconception is that an ISMS is just a folder of security policies. It’s not. While documentation is part of it, the ISMS is a living system — a set of ongoing processes and controls that continuously manage information risk.
The three components of a functioning ISMS are:
- People — arguably the most important element. Humans design, implement, and maintain the system. They’re also the most common point of failure.
- Processes — the procedures and workflows that guide how information is handled, incidents are reported, risks are assessed, and improvements are made.
- Technology — the tools that enforce and enable security, from encryption software to access management systems. These must be regularly reviewed and updated as threats evolve.
How It Works: The Plan-Do-Check-Act Cycle
ISO 27001 doesn’t treat security as a one-time project. Instead, it uses the Plan-Do-Check-Act (PDCA) cycle — a continuous improvement model used across many management standards.
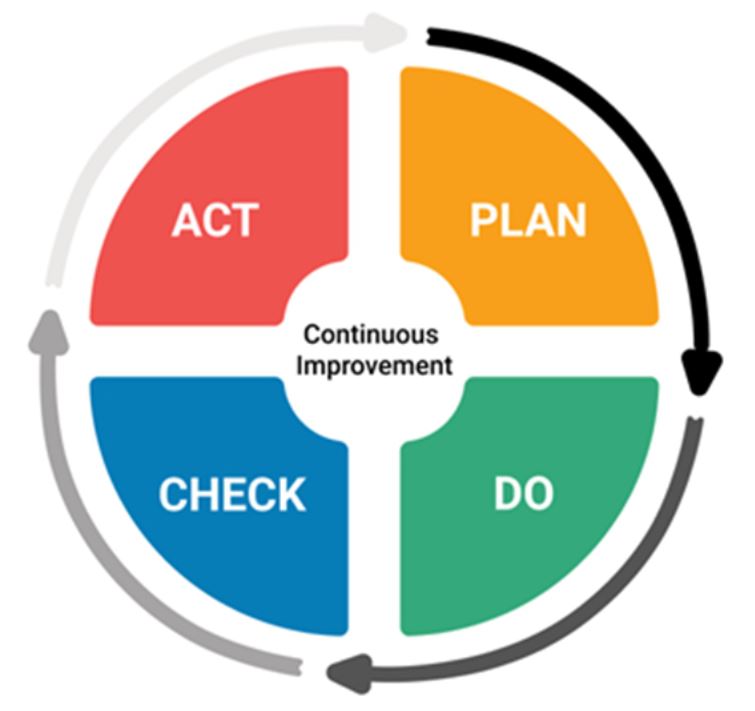
Plan: Define your security objectives, identify risks, and develop the policies and procedures needed to manage them.
Do: Implement those plans — execute the processes, train your team, and put controls in place.
Check: Monitor how well your ISMS is working. Measure performance, conduct internal audits, and compare results against your objectives.
Act: Based on what you learned, make improvements. Fix gaps, address non conformities, and refine your approach for the next cycle.
This ongoing loop ensures that ISO 27001 is not a “set it and forget it” certification, but a continuously improving security posture.
The 7 Clauses: The Core Requirements

For an organization to become ISO 27001 certified, it must implement Clauses 4 through 10 — seven requirements that cover the full lifecycle of an ISMS.
Clause 4 — Context of the Organization Before you can protect something, you need to understand it. This clause requires organizations to assess their internal environment (culture, structure, existing policies) and external environment (regulatory landscape, industry threats, social and technological trends) to define the scope of the ISMS. Who are your stakeholders? What are their expectations? What are your legal obligations?
Clause 5 — Leadership Security doesn’t stick without buy-in from the top. This clause requires that senior management actively demonstrate commitment to the ISMS — not just sign off on a document, but drive a cultural shift. An information security policy must be approved at the leadership level, and roles and responsibilities must be clearly assigned throughout the organization.
Clause 6 — Planning Organizations must identify and assess information security risks, set measurable objectives, and create specific plans for achieving them. These objectives should align with broader business goals and be regularly reviewed for relevance.
Clause 7 — Support Implementing security requires resources — and this clause ensures that people are given the time, training, and tools to do their jobs. Security responsibilities should be embedded into ongoing roles, not treated as a side project.
Clause 8 — Operation This is where planning meets reality. Clause 8 requires organizations to conduct regular risk assessments and implement appropriate controls. Importantly, it requires documentation of these evaluations as ongoing evidence of compliance — not just a one-time check.
Clause 9 — Performance Evaluation Once the ISMS is running, it needs to be measured. Internal and external audits assess whether the system is effective. Management reviews these findings to determine whether the ISMS is performing as intended or needs adjustment.
Clause 10 — Improvement When a gap, nonconformity, or opportunity for improvement is identified, it must be documented, prioritized, and addressed within a defined timeframe. Continual improvement is not optional — it’s baked into the standard.
Annex A: The Security Controls
Beyond the seven clauses, ISO 27001 includes Annex A — a reference catalogue of security controls organized into four categories:
- Organizational Controls — policies, roles, supplier security, incident management
- People Controls — hiring practices, training, disciplinary processes
- Physical Controls — secure areas, equipment protection, clear desk policies
- Technological Controls — access control, encryption, malware protection, logging
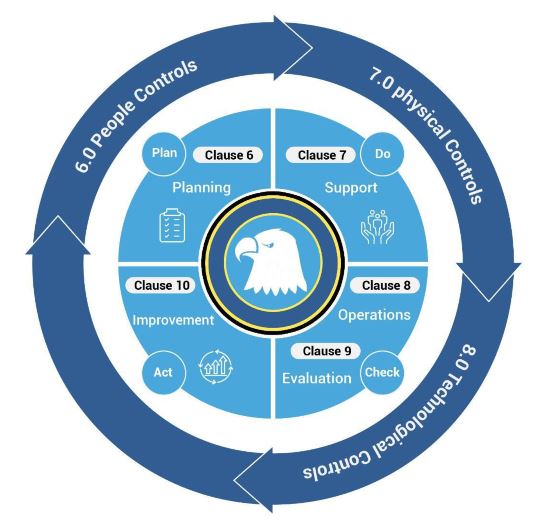
Organizations don’t necessarily implement every control in Annex A. Instead, they conduct a risk assessment and select the controls most relevant to their specific context. This flexibility is part of why ISO 27001 works for organizations of all sizes, from small businesses to global enterprises.
The Benefits of ISO 27001
Why invest the time and resources in achieving certification? The benefits go well beyond a certificate on the wall.
Stronger cybersecurity posture. The most direct benefit is reducing the risk of a costly breach. The structured risk management process helps organizations identify vulnerabilities before attackers do.
Regulatory alignment. ISO 27001 naturally aligns with major regulations including GDPR and the NIS Directive. While it’s not a direct compliance substitute, implementing its best practices significantly reduces legal and regulatory exposure.
Reputation and trust. Certification signals to clients, partners, and regulators that your organization takes security seriously. In competitive industries, this can be a meaningful differentiator.
Organizational clarity. Implementing ISO 27001 often forces organizations to clarify roles, reduce duplication of effort, and make more informed decisions about where to invest in security — often resulting in cost savings over time.
Reduced audit burden. With an established, certified ISMS, organizations can reduce the frequency and cost of customer-driven audits, since the certification itself serves as evidence of effective security practices.
ISO 27001 vs. ISO 27002 and ISO 27005
ISO 27001 doesn’t exist in isolation. It’s part of the broader ISO 27000 family of standards:
- ISO/IEC 27001 defines what your ISMS must accomplish — the framework and requirements.
- ISO/IEC 27002 provides implementation guidance — how to apply the security controls listed in Annex A.
- ISO/IEC 27005 focuses on risk management — a dedicated guide to identifying, assessing, and treating information security risks.
In practice, organizations pursuing ISO 27001 certification often reference all three together.
Is ISO 27001 Right for Your Organization?
ISO 27001 is designed to be scalable. A 20-person technology startup and a 50,000-employee multinational can both implement it — the scope of the ISMS is defined by the organization based on its own context and needs.
That said, it does require genuine commitment: from leadership, from IT and security teams, and from the broader organization. The PDCA cycle means the work doesn’t end at certification — it must be sustained and improved over time.
If your organization handles sensitive customer data, operates across multiple jurisdictions, works with regulated industries, or simply wants a credible, proven framework for managing security risk — ISO 27001 is worth serious consideration.
Final Thoughts
ISO 27001 can sound like bureaucratic alphabet soup to the uninitiated. But at its heart, it’s a practical and thoughtful answer to a genuine challenge: how do organizations protect the information that matters most, in a threat landscape that never stops changing?
By combining clear requirements, ongoing risk management, leadership accountability, and a culture of continuous improvement, ISO 27001 gives organizations a solid foundation — not just to pass an audit, but to genuinely operate more securely.
That’s what makes it the most recognized information security standard in the world.
