Security is a core design principle of the OPC Unified Architecture (OPC UA). Unlike earlier industrial communication technologies, OPC UA integrates security mechanisms directly into the protocol architecture to protect communication between industrial devices, control systems, and enterprise applications.
The conceptual security framework is defined in IEC TR 62541-2, while implementation details are distributed across other parts of the specification including IEC 62541-4 (Services) and IEC 62541-6 (Communication Mappings). These standards define how secure channels are established, how applications authenticate each other, and how data integrity and confidentiality are maintained across industrial networks.
The OPC UA security model addresses threats that commonly affect industrial control systems, including:
- Unauthorized access to automation systems
- Message tampering during transmission
- Replay attacks
- Impersonation of clients or servers
- Man-in-the-middle attacks
To mitigate these threats, OPC UA uses a multi-layer security architecture based on certificate authentication, cryptographic algorithms, secure sessions, and message integrity verification.
Table of Contents
OPC UA Security Architecture
The OPC UA security architecture separates responsibilities into several layers. Each layer contributes to protecting communication and enforcing security policies.
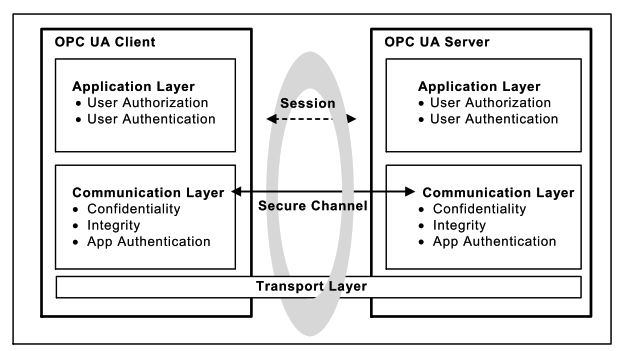
Application Layer
The application layer is responsible for:
- user authentication
- user authorization
- access control
Authentication mechanisms supported at this layer include username/password, certificates, and enterprise authentication systems.
Communication Layer
The communication layer ensures secure message exchange between clients and servers by providing:
- confidentiality through encryption
- integrity through digital signatures
- application authentication through certificates
Transport Layer
The transport layer provides network connectivity using protocols such as:
- OPC UA TCP
- HTTPS
- WebSockets
Security mechanisms are applied above the transport layer to ensure protocol independence.
OPC UA Secure Channel
The Secure Channel is responsible for protecting messages exchanged between OPC UA applications.
Secure channels provide three fundamental protections:
- message encryption
- message integrity
- message sequence validation
A secure channel is created using the OpenSecureChannel service defined in the OPC UA services specification. During channel establishment, the client and server negotiate security parameters and exchange cryptographic keys.
Once the secure channel is established, all messages exchanged between client and server are protected according to the selected security policy.
Secure channels also use security tokens, which contain encryption keys and have a limited lifetime. Tokens must be periodically renewed to maintain secure communication.
OPC UA Certificate Infrastructure
OPC UA uses X.509 digital certificates and a Public Key Infrastructure (PKI) to establish trust between communicating applications.
Each OPC UA application instance possesses a certificate that contains:
- application URI
- public key
- certificate issuer
- validity period
- digital signature
Certificates are issued by a Certificate Authority (CA) and stored in the application’s certificate store.
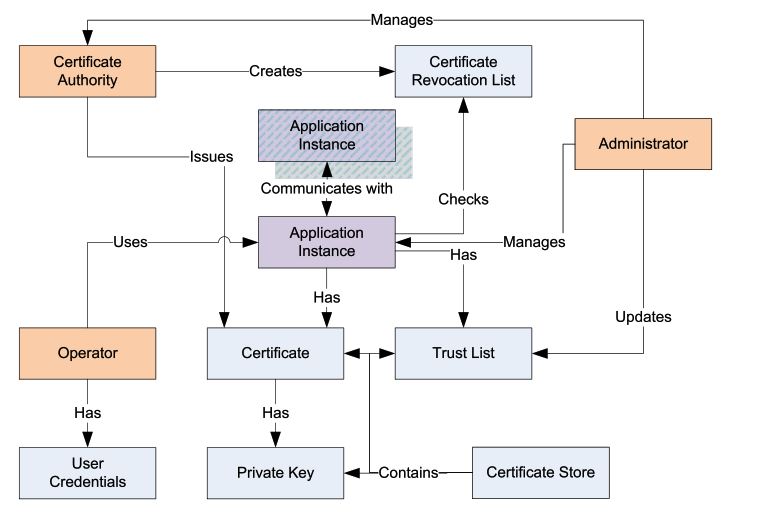
The diagram above illustrates the relationships between the main PKI components in OPC UA security architecture.
Certificate Authority (CA)
The Certificate Authority is responsible for:
- issuing application certificates
- managing certificate revocation lists (CRL)
- establishing the trust chain used to validate certificates
Application Instance
An OPC UA application instance represents a client or server implementation that participates in secure communication.
Each instance:
- owns a certificate
- contains a private key
- maintains a trust list of accepted certificates
Trust List
The trust list contains certificates or certificate authorities that the application trusts.
During connection establishment, the application verifies whether the remote certificate exists in the trust list.
If the certificate is not trusted, the connection is rejected.
Certificate Revocation List (CRL)
The CRL contains certificates that have been revoked by the certificate authority.
Before establishing communication, OPC UA applications check whether a certificate appears in the CRL.
If the certificate is revoked, the connection must be rejected.
Certificate Store
The certificate store is the repository where the application stores:
- certificates
- private keys
- trusted certificates
Administrator Role
Administrators manage:
- trust lists
- certificate stores
- certificate revocation lists
They ensure that only trusted applications are allowed to communicate.
CA-Based Certificate Handling
In many industrial environments, certificate management is performed using a Public Key Infrastructure (PKI) with a central certificate authority.
The typical workflow is:
- A certificate authority generates a root certificate.
- The CA issues certificates for OPC UA servers and clients.
- Certificates are installed in the application certificate stores.
- The client verifies the server certificate using the CA trust chain.
- Secure communication is established if the certificate is trusted.

Using a centralized CA simplifies certificate management and improves scalability for large industrial deployments.
Manual Certificate Trust Management
In smaller installations, certificate trust may be established manually without a certificate authority.
In this approach:
- The server generates its certificate.
- The client generates its certificate.
- An administrator exports the certificates.
- Certificates are manually installed into each system’s trust list.

Although manual certificate handling works for small deployments, it becomes difficult to manage in large industrial networks.
OPC UA Security Modes
OPC UA defines three message security modes.
| Security Mode | Description |
|---|---|
| None | No cryptographic protection |
| Sign | Messages are digitally signed |
| SignAndEncrypt | Messages are signed and encrypted |
Industrial deployments typically require SignAndEncrypt mode to ensure both confidentiality and integrity.
Cryptographic Algorithms
OPC UA supports both asymmetric and symmetric cryptography.
Asymmetric Cryptography
Used during the initial handshake and authentication.
Typical algorithms include:
- RSA encryption
- RSA digital signatures
Symmetric Cryptography
Used for efficient message encryption once the secure channel has been established.
Typical algorithms include:
- AES encryption
Hash Functions
Used for integrity verification.
Typical algorithms include:
- SHA-256
The specific algorithms used depend on the selected security policy.
OPC UA Security Policies
Security policies define which cryptographic algorithms and key lengths are used during communication.
Common OPC UA security policies include:
| Security Policy | Description |
|---|---|
| Basic128Rsa15 | Legacy policy |
| Basic256 | AES-256 encryption |
| Basic256Sha256 | Modern secure policy |
Security policies are advertised by OPC UA servers during the endpoint discovery process.
Clients select the most secure supported policy before establishing communication.
User Authentication
After a secure channel is established, the client creates a session and authenticates the user.
Supported authentication mechanisms include:
- Anonymous access
- Username and password
- X.509 certificates
- Kerberos authentication
Authentication occurs during the ActivateSession service.
Session Security
Sessions provide an application-level communication context between OPC UA clients and servers.
Each session includes a SessionAuthenticationToken, which uniquely identifies the authenticated session.
The token is included in every service request to ensure that requests originate from the authenticated client.
This mechanism prevents session hijacking and unauthorized service execution.
Security Best Practices for Industrial Systems
To ensure secure OPC UA deployments, several best practices should be followed:
- Use SignAndEncrypt security mode
- Disable legacy security policies
- Implement a certificate authority
- Maintain updated certificate revocation lists
- Restrict anonymous access
- Segment industrial networks
These practices significantly reduce the risk of cyberattacks on industrial control systems.
Conclusion
The OPC UA security architecture defined in IEC TR 62541-2 provides a comprehensive framework for securing industrial communication systems.
By integrating:
- certificate-based authentication
- encrypted communication
- secure session management
- strong cryptographic algorithms
OPC UA enables secure and interoperable communication across distributed industrial environments.
As industrial systems continue to adopt Industry 4.0 and Industrial IoT architectures, OPC UA security mechanisms play a critical role in protecting industrial infrastructure from cybersecurity threats.
